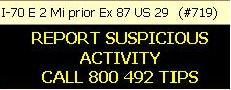
As I drove by this the other morning, I thought, “Yeah, right. What’s ‘suspicious’? If the traffic was moving a bit faster… now that would be suspicious.”
Then I realized, I was mistaken to be so derisive. Because, while we cannot define suspicious activity, I think we often know it when we see it. I mean, by definition, it is activity that arouses uncertainty or seems strangely out of place. It is directly linked to feelings. Suspicion is subjective. It is not easily measurable. And that is just fine.
This is why user education is still a viable part of a network security defense. Surely, security mechanisms such as firewalls, antivirus protection, etc. don’t forget and so are more reliable that just educating the user — whose main task usually has nothing to do with security — to avoid doing bad things. But, users are very good at recognizing when — as Miss Clavel, of the Ludwig Bemelmans’ classic Madeline children’s books, noted — “Something is not right!” So, we remind our users that they should report suspicious activity. Such as people with masks over their heads approaching the building? I suppose so. But, in our realm we’re more interested in the network seeming to run slower than usual, the desktop computer crashing (more than it usually does, perhaps), “phishing” attempts, increased disk activity when nothing seems to be happening, or computer performance degradation.
Foolproof? No. Cost-effective? It depends. (A very important security answer.) It depends on how much it costs. In user education, a small amount of money goes a long way. It’s like those highway signs. Will they hinder a terrorist attack? Maybe not. But… maybe. When securing your network, someone will probably notice when something is amiss. It doesn’t cost very much to help them remember what to do.
| Fred Wamsley, CISSP and principal with Beryllium Sphere LLC, commented, “A CERT study backs up your argument. They recently released a study of insider attacks, and looked into how they were detected. Mostly it was not security personnel who spotted the fraud/sabotage/whatever. Usually a customer or another employee noticed something out of the ordinary.” |

